Securityheaders.io: How Safe is Your Web Space?
Security is often neglected by website owners. Everything is cared for, new features are implemented and a neat design is created. Then one day, your website gets hacked. To prevent this unpleasant scenario, a strategy and some effort is necessary. If you happen to own your own server, that's just another reason to take care of security. In many cases, this is rather simple. To help you protect your website, I'll now introduce you to the online tool securityheaders.io, which shows you the weaknesses of your server or shared space, and provides advice on how to remove them.
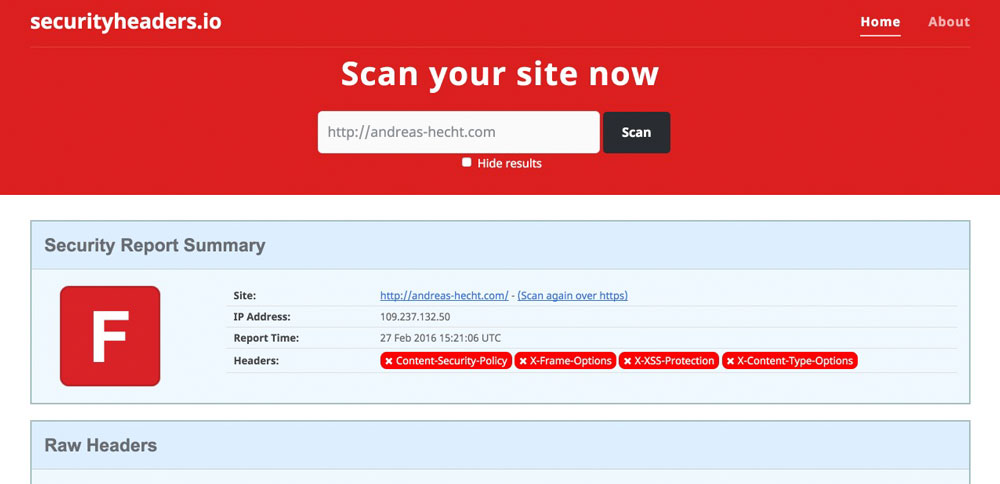
 Securityheaders.io is the name of the online service that can determine how safe your server is, judging by the sent HTTP response headers. Of course, there are many services that can analyse HTTP response headers. But the unique thing about securityheaders is its rating system, into which it sorts the results. The system orders the results in an area from A to F. Here; A is a perfectly protected server while F is given out for destitute protection.
The service and its operator Scott Helme want to contribute to more safety on the internet. Not only does it analyze the response headers, but it also gives solid advice on how to remove the security issues. Sending the right HTTP response headers leads to much better safety and should thus be looked into. This takes relatively little time. However, the potential increase in security is tremendous.
Securityheaders.io is the name of the online service that can determine how safe your server is, judging by the sent HTTP response headers. Of course, there are many services that can analyse HTTP response headers. But the unique thing about securityheaders is its rating system, into which it sorts the results. The system orders the results in an area from A to F. Here; A is a perfectly protected server while F is given out for destitute protection.
The service and its operator Scott Helme want to contribute to more safety on the internet. Not only does it analyze the response headers, but it also gives solid advice on how to remove the security issues. Sending the right HTTP response headers leads to much better safety and should thus be looked into. This takes relatively little time. However, the potential increase in security is tremendous.
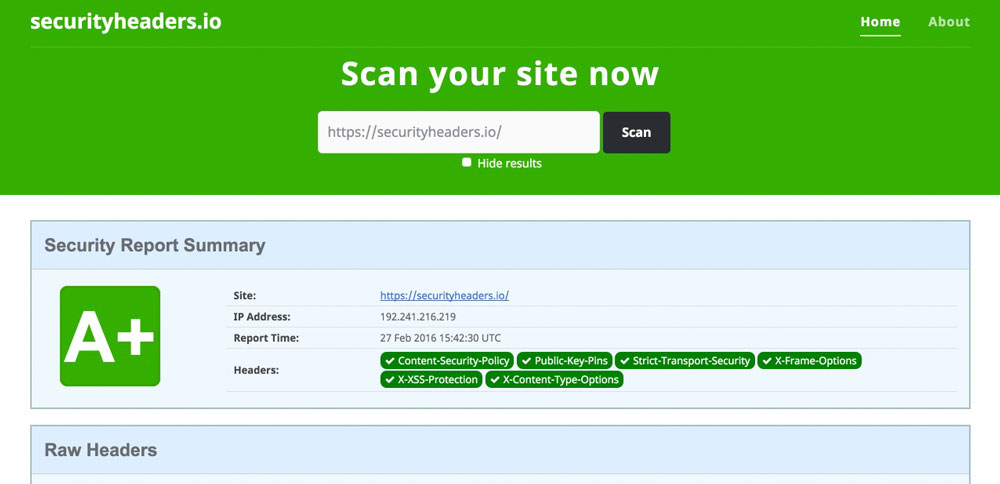
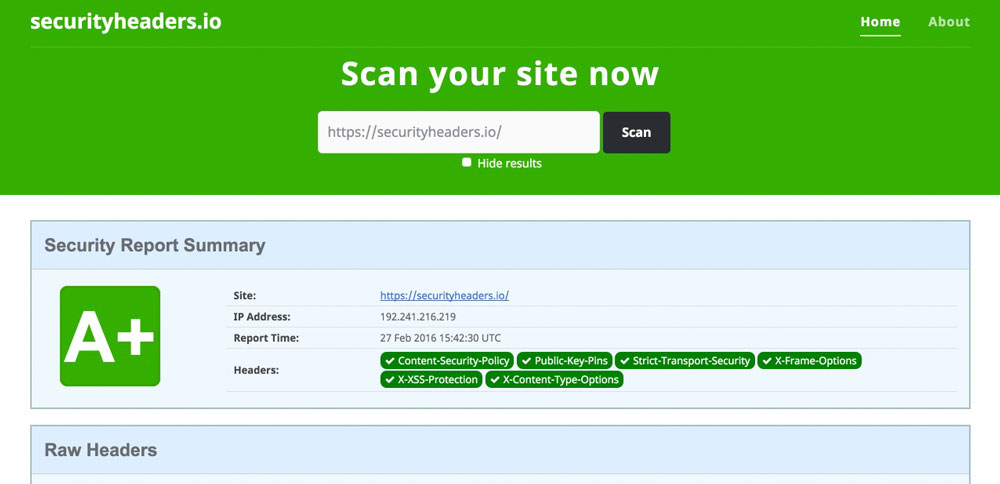
 A potentially poor security is not only marked with an F but also colored in red to visualize the safety breach. Very safe servers are colored green, as shown in this scan of the securityheaders website.
A potentially poor security is not only marked with an F but also colored in red to visualize the safety breach. Very safe servers are colored green, as shown in this scan of the securityheaders website.
 My Website's Missing Response Headers
There are links for each result, which are providing additional substantial articles on each of the areas. This way, you can learn a lot about the respective headers. Afterwards, you'll know exactly what to do and especially, why you should do it. Behind the missing header »Content-Security-Police«, you'll find the article "Content Security Policy - An Introduction." Additionally, there are good explanations on this area in other languages.
My Website's Missing Response Headers
There are links for each result, which are providing additional substantial articles on each of the areas. This way, you can learn a lot about the respective headers. Afterwards, you'll know exactly what to do and especially, why you should do it. Behind the missing header »Content-Security-Police«, you'll find the article "Content Security Policy - An Introduction." Additionally, there are good explanations on this area in other languages.
Securityheaders.io - Analysis of the HTTP Headers
 Securityheaders.io is the name of the online service that can determine how safe your server is, judging by the sent HTTP response headers. Of course, there are many services that can analyse HTTP response headers. But the unique thing about securityheaders is its rating system, into which it sorts the results. The system orders the results in an area from A to F. Here; A is a perfectly protected server while F is given out for destitute protection.
The service and its operator Scott Helme want to contribute to more safety on the internet. Not only does it analyze the response headers, but it also gives solid advice on how to remove the security issues. Sending the right HTTP response headers leads to much better safety and should thus be looked into. This takes relatively little time. However, the potential increase in security is tremendous.
Securityheaders.io is the name of the online service that can determine how safe your server is, judging by the sent HTTP response headers. Of course, there are many services that can analyse HTTP response headers. But the unique thing about securityheaders is its rating system, into which it sorts the results. The system orders the results in an area from A to F. Here; A is a perfectly protected server while F is given out for destitute protection.
The service and its operator Scott Helme want to contribute to more safety on the internet. Not only does it analyze the response headers, but it also gives solid advice on how to remove the security issues. Sending the right HTTP response headers leads to much better safety and should thus be looked into. This takes relatively little time. However, the potential increase in security is tremendous.
Many Servers are Potentially Unsafe
If you play around with the online tool for a bit, you should quickly notice that the majority of the tested servers are potentially endangered. No matter which domain I entered and checked, the shown result was always F. Even for my own websites. Until now I assumed that a managed server or a managed WordPress hosting was secure and that you didn't need to take care of that area. Now I know that managed doesn't automatically mean safe. Shared hosting systems are not any safer, as I got an F there as well.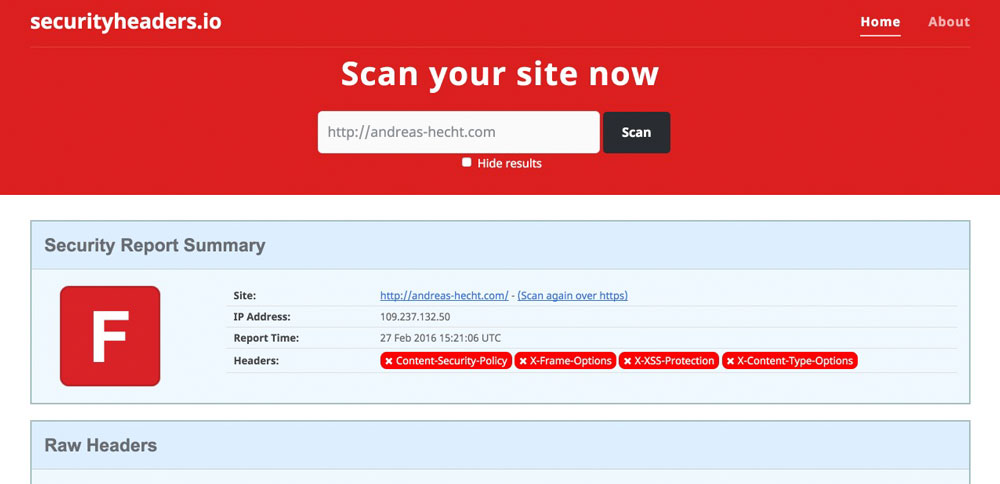 A potentially poor security is not only marked with an F but also colored in red to visualize the safety breach. Very safe servers are colored green, as shown in this scan of the securityheaders website.
A potentially poor security is not only marked with an F but also colored in red to visualize the safety breach. Very safe servers are colored green, as shown in this scan of the securityheaders website.
Good Explanations of the Results and Tips on Improvements
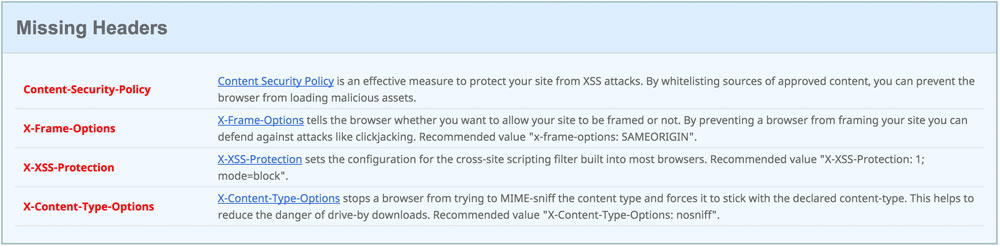
Every (bad) scan result shows exactly which HTTP response headers are missing. A short description tells you, why these headers are necessary, and what can happen if they are missing.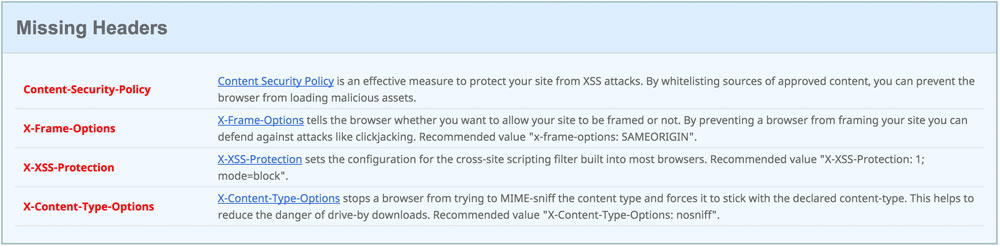 My Website's Missing Response Headers
There are links for each result, which are providing additional substantial articles on each of the areas. This way, you can learn a lot about the respective headers. Afterwards, you'll know exactly what to do and especially, why you should do it. Behind the missing header »Content-Security-Police«, you'll find the article "Content Security Policy - An Introduction." Additionally, there are good explanations on this area in other languages.
My Website's Missing Response Headers
There are links for each result, which are providing additional substantial articles on each of the areas. This way, you can learn a lot about the respective headers. Afterwards, you'll know exactly what to do and especially, why you should do it. Behind the missing header »Content-Security-Police«, you'll find the article "Content Security Policy - An Introduction." Additionally, there are good explanations on this area in other languages.
How HTTP Response Headers Increase Our Server's Safety
The »Content-Security-Police-Header« is a good protection against the problem called cross-site scripting. So-called XSS or cross-site scripting attacks are some of the biggest security threats for web applications. Here, protection against code brought into the website from outside is required. The »Content-Security-Police« header allows you to determine which scripts can be accessed from outside. The default setting only allows for the execution of scripts that are on the local server. Additionally, define all scripts which have to be accessed. Google Adsense and Google Analytics Code, for example. Every other - external - code is ignored, and thus, not executed. This is the case for images, frames and videos as well. Meaning all things that are not on your own server. Setting the exceptions is tedious. However, you'll be rewarded with a tremendous increase in safety.Other Response Headers
The scan of my personal website resulted in four missing HTTP response headers. Among others, the already mentioned »Content-Security-Header«, the »X-Frame-Options-Header«, the »X-XSS-Protection-Header«, and the »X-Content-Type-Options-Header«. The »X-Frame-Options-Header« protects your website from being executed in a frame. There are people on the web that like to adorn themselves with borrowed plumes. These people create like to integrate other websites via iFrames. This way, they provide good content without writing it themselves. The »X-XSS-Protection-Header« configures the internal "Cross-Site-Scripting-Filter", which is integrated into most browsers already. The recommended configuration "X-XSS-Protection: 1; mode=block" protects your visitors from attacks on their computers. The following browsers support the filter: Internet Explorer, Chrome, and Safari (Webkit). The »X-Content-Type-Options-Header« can only set the value "nosniff". It prevents Internet Explorer and Google Chrome from searching for MIME types different from the ones defined by the declared content type (text/HTML for example). Google Chrome is also prevented from downloading extensions. Thus, so-called drive-by download attacks are not possible anymore. Your computer can not be infected with malicious code. Of course, this only applies to the website that set this response header.Conclusion
The online service securityheaders can increase the security significantly. Not only were we able to secure our own server by using the appropriate HTTP response header, but we also improved our visitor's safety. The online tool shows exactly where the security issues are and how they can be fixed.Related Links:
- securityheaders.io - Analyse your HTTP response headers
- Hardening your HTTP response headers
- Security HTTP Headers

how can i clean SQL injection showing in google and bing,Yahoo my website has been hacked but i have scanned and cleaned all Word press Files any help to clean showing problem in this networks,how to cleab up CMS SQL Injection Vulnerability